🔎🦶Enumeration/Foothold
Search is a realistic (awesome) corporate-environment Hard box from HTB created by dmw0ng. You start by finding a corporate website running on Ports 80/443. Going through HTTPS allows you to find a hidden sub-domain. The website itself has a bunch of users and some credentials hidden in an image. You use these creds to find all the users on the domain and export the domain controller with python-bloodhound. Reviewing the export on Bloodhound, you can see that WEB_SVC is Kerberoastable. We use GetUserSPNs to get the hash and use john to crack it. We spray the domain-controller with CrackMapExec and the new password giving us access to Edgar Jacobs’ account. Spidering his account we find an Excel file which we remove the security on for additional passwords. A final password spray gives us access to Sierra Frye’s account. Her account has a .PFX file we crack for access to /staff/ on the website. Finally use her account with gMSADumper and a web-based PowerShell session to alter Tristan Davie’s account for root.
Before I begin each machine I kick off a full port scan with RustScan and pipe the open ports found into NMAP:
Once it completes I take the scan and convert it to HTML. I do this as force of habit from client engagements:
Reviewing the results as they come in I could see that this was mostly likely a Windows server as SMB and kerberos are running. I could also see that Port 80/443 were open so I started with them. Navigating over to Port 80 showed a company website (and not a standard boilerplate template you would normally see on CTFs).

Search Corporate website showing Research heading.
‘Our Team’ showed multiple employees so I created a users file with all the names formed in the way of a typical email: lastnamef, firstnamel, firstname.lastname figuring it will come in handy for password sprays or username hunting later.

Our Team area showing multiple possible accounts to exploit.
Later on during my enumeration I also saw a username (Hope Sharp) and password IsolationIsKey? within an image on the website. This took a while as I was thinking more stock photos on a corporate website and not Where’s Waldo:
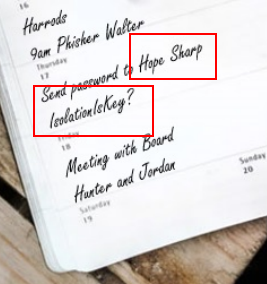
Find the password well scrolling through the site…
On the HTTPS portion of the website, the certificate showed a sub-domain I didn’t know about which I added to my hosts:

research.search.htb sub-domain found.
Visiting the new sub-domain sent me to the same website so I moved on. Going to an invalid page /MyBrainHurts shows an error page which looked like IIS. I kicked off a feroxbuster for directories and a specific one for IIS directories:
Using this I was able to determine that the organization Search, uses firstname.lastname for their accounts. Much later on I found the password in the image above and used it find a valid user account:
I took the valid account and used CrackMapExec to list all the employees on the domain and export:
Next, I used bloodhound-pythonalongside the valid account to export the domain controller:

Finding the WEB_SVC account under Kerberoastable Accounts.
Reviewing the export in BloodHound I was able to see that the web_svc account was Kerberoastable. I used impacket-GetUsersSPNs and the valid account to grab the hash:
I took the hash and used john to crack it which gives me the password @3ONEmillionbaby. I went back to the certsrv rabbit hole which gives me nothing. I then proceed to password spray the employees with the new password.
I then use crackmapexec and its spider-plus function to pull a list of files the new account has access too:
Which the following stuck out from the export:
I downloaded the file to my vm and opened it. This next part was extremely easy because I watched IPPSEC – HackTheBox – Developer which is funny that this would be on two boxes so close together? I unzipped the Excel file and removed the protection string from sheet2.xml and re-zipped the files (not folder). Opening the sheet provides the following passwords:
| First Name | Last Name | Password | Username |
|---|---|---|---|
| Payton | Harmon | ;;36!cried!INDIA!year!50;; | Payton.Harmon |
| Cortez | Hickman | ..10-time-TALK-proud-66.. | Cortez.Hickman |
| Bobby | Wolf | ??47^before^WORLD^surprise^91?? | Bobby.Wolf |
| Margaret | Robinson | //51+mountain+DEAR+noise+83// | Margaret.Robinson |
| Scarlett | Parks | ++47″ | building” |
| Eliezer | Jordan | !!05_goes_SEVEN_offer_83!! | Eliezer.Jordan |
| Hunter | Kirby | 27%when%VILLAGE%full%00 | Hunter.Kirby |
| Sierra | Frye | 49=wide=STRAIGHT=jordan=2818 | Sierra.Frye |
| Annabelle | Wells | 95~pass~QUIET~austria~77 | Annabelle.Wells |
| Eve | Galvan | //61!banker!FANCY!measure!25// | Eve.Galvan |
| Jeramiah | Fritz | ??40:student:MAYOR:been:66?? | Jeramiah.Fritz |
| Abby | Gonzalez | &&75:major:RADIO:state:93&& | Abby.Gonzalez |
| Joy | Costa | 30venusBALLoffice42 | Joy.Costa |
| Vincent | Sutton | 24&moment&BRAZIL&members&66 | Vincent.Sutton |
I created a users_excel and passwords_excel based off the export above and added in previously found passwords for good measure. I then ran both lists using crackmapexec:
🔝Escalation to Root
I logged into Sierra’s account via SMB and grabbed the first flag as well as her entire profile. Inside /sierra.frye/Downloads/Backups/ I could see two files: staff.pfx and search-RESEARCH-CA.p12. After finding out I could import them into Firefox I attempted to import the staff.pfx file:

Importing the certificate to FireFox requires a password.
A short Google later lead me to the following tool – crackpkcs12 – SourceForge
Reviewing BloodHound I could see Sierra Frye’s account had CanPSRemote to RESEARCH.SEARCH.HTB. I could also see the account has ReadGMSAPassword:

Bloodhound showing the RESEARCH.SEARCH.HTB had CanPSRemote capability and ReadGMSAPassword.
Remembering the staff directory found earlier I navigated to it on Firefox via HTTPS which displays a PowerShell web access. I login using Sierra Faye’s credentials:

Referencing back to the previously found /staff/ directory.

Windows PowerShell Web Access on the /staff/ directory.
Within the PowerShell session I use PayloadsAllTheThings – GMSA which I also used on HTB – Intellgence.
Reviewing the instructions, I put in all the commands from the article and then tried a which validated I am running as BIR-ADFS-GMSA! Next, I referred back to BloodHound which stated I have the GenericAll permissions to the Tristan Davies account. I use the GenericAll permissions to reset user accounts password and grab the root flag:

Windows PowerShell Web Access on RESEARCH.SEARCH.HTB.
I then use CrackMapExec to grab all the hashes and grab the root flag from the SMB share:




